Running a business is stressful, but so is thinking about a future where that business (and its data) no longer exists. If you’re not careful with your preparedness, you could stare down a disaster with no hopes of recovery. This is why we urge you to take proactive action now—so you can prevent these kinds of scenarios from taking your business off the market for good.
Telesys Voice and Data Blog
I feel like we’ve been talking a lot about the horrifying cybersecurity threats that loom over our heads, and thought it might be nice to really appreciate just how gosh-darn cool some of these devices we all have can be instead.
We’re always talking about boosting productivity and the role your technology has in that quest. What we don’t always talk about is how boosting innovation can help free up your employees to produce better results. It’s the same technology, and it can have multiple benefits. In this week’s blog, we’ll discuss how focusing on how these two thoughts can be one and the same.
For modern organizations that depend highly on their technology, nothing is quite so scary as an event that can completely marginalize its ability to operate. This doesn’t need to be a fire, flood, or some other major cataclysm; it could be something as simple as some of your old IT fails and you’re not ready for it. This week, we thought we’d briefly go through what a catastrophic failure looks like and some steps you can take to keep your business from experiencing one.
Businesses that depend on their technology try to stick with it as long as they can so as to not incur large unnecessary costs. Ironically, that may be the thing that is causing a lot of those costs. Today, we thought we would take a look at a couple of variables that can let you know it’s time to upgrade away from your current technology.
Despite hearing about a constant stream of cyberattacks over the past few years—most of which cause millions of dollars of damage to businesses—it might still be difficult for you to justify spending a lot of money on your business’ cybersecurity plans. There is a finite amount of capital to go around and many times CIOs and network administrators will be rebuffed by management when asking for money to spend on cybersecurity. Today, we thought we’d discuss three ways that you can spend on cybersecurity initiatives and not feel like you are throwing your money down the drain.
In any business, the capacity to collaborate is critical to success. In order to do so most optimally, it helps to carry out a few preliminary and overarching practices. Let’s go over a few such practices to help bring your team’s collaborative activities together.
Did you know that people tend to spend an average of 3-5 hours on their phones every day? The smartphone might be one of the most useful modern tools out there, but it can get in the way of running your business if you let it. Here are a couple of ways you can get the most out of your smartphone for business purposes.
It might be an understatement to suggest that things don’t always go smoothly in business. The truth is that when one problem is solved, another is often created. This is why we lean on our technology. These “solutions” are intended to fix many of the speedbumps, but that doesn’t mean that choosing, deploying, and supporting these systems don’t come with some problems as well. Today, we look at three reasons an IT project could fail.
There is a microprocessor shortage influencing all kinds of businesses around the globe, and it’s only going to get worse following the Russian invasion of Ukraine. Ukraine produces somewhere between 45 and 54 percent of the world’s semiconductor-grade neon, something which is absolutely crucial to the creation of microchips. The invasion has put a halt to neon-refinement companies Ingas and Cryoin, and as you can imagine, this puts a massive strain on an already struggling supply chain.
Laptops are pretty great, I think we can all agree, simply due to their portability. Having said that, the one-screen situation that laptops bring with them can certainly get in the way of productivity—particularly for those who are used to using more than one. Let’s discuss why an additional display is so helpful, and what your options may be for hooking one up to your laptop.
Try as we might, we can’t prevent all computer issues from occurring—for instance, there’s not much that we can do if a stick of RAM dies, at least, not remotely. However, if you’re stuck with a broken computer and need to bring it in for repair work, there are a few things we recommend you do.
As statistics for cybercrime surge, it’s important to remember that your organization must do all that it can to protect itself. There is, however, a C-suite position that almost exclusively focuses on this task: the chief information security officer, or CISO. Many enterprises have individuals dedicated to the sole task of securing their organization, but smaller businesses might find themselves lagging behind in this regard due to no fault of their own.
Bookmarks are an essential part of being productive with your Internet browser, but what happens when you switch to a different one, like Google Chrome? Do you have to manually add all of your bookmarks back to the browser? Nope! Let’s go over how you can import your bookmarks directly to Google Chrome and save some time.
Cloud computing is being used by nearly everyone nowadays, and most of the time it presents a lot of value that can’t be found with purchasing, managing, and maintaining an in-house computing infrastructure. As an organization begins moving more and more of their computing to the cloud, there is a situation that arises that industry professionals call “cloud sprawl”.
Nothing changes the fortunes of a business faster than having clear lines of communication, especially after operating with less-than-effective communications for a time. Today, there are options that provide businesses with enterprise-level communications without the massive price tag and commitments that they typically bring.
As time has passed, cybersecurity attacks have become another way some organizations and nations engage in warfare. You can argue that there is a war going on at all times in cyberspace while hackers—many of which are sponsored by government agencies—try to outdo security researchers at all turns. One such scenario sees customers in the United States and Israeli defense technology sectors becoming the target of “password spraying.”
Sometimes you might encounter situations where your network is limited in the amount of data it can process at any given time. The unfortunate truth is that it can be difficult to identify exactly what the problem is that is causing the slowdown, but one of the most common issues—the network bottleneck—is a pretty safe bet. But what exactly is a bottleneck, and what can be done to solve it?
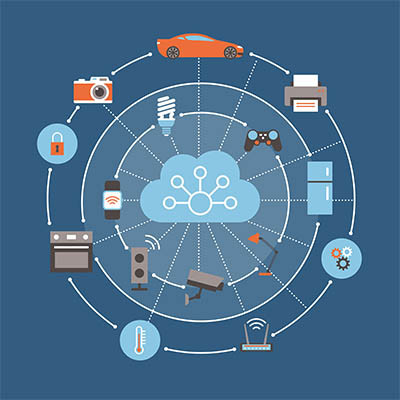
Smart devices have brought about unprecedented amounts of connectivity in aspects of running a business or owning a home that never could have been dreamed of in the past. People can now unlock their front doors, turn up their thermostats, and even switch the lights on and off through their smartphone. Unfortunately, the part that people don’t like to talk about with these applications and devices is security—big surprise, right?
Artificial intelligence, commonly known as AI, is used in several different ways in various industries, but one of the most impactful has been with cybersecurity and its automation. On the other hand, however, are the hackers who use AI in ways that fly in the face of the efforts of these cybersecurity professionals and use AI for cybercrime. What are some ways that AI is used in cybercrime, and why is it so scary for businesses to handle?
Mobile? Grab this Article!
Tag Cloud