Special text characters are an integral part of typing. For the most part, however, they are not something that your normal, run-of-the-mill keyboard or laptop keypad is able to access easily. Luckily, for Windows 10 users, there is a shortcut that allows you to access all sorts of special characters.
Telesys Voice and Data Blog
Consultation is one of those words that you take for granted because you see it everywhere. Think about it, most businesses that provide a professional service offers some semblance of consultation. For the small business owner, can you really afford to pay premium prices to “experts” for them to give you their so-called professional opinion? Besides, what do service providers mean when they use the term “consultation”?
In the traditional sense, a consultation is a meeting to discuss a contracted issue. To that end the consultation provides the opportunity for a party that is dealing with problems to get a professional opinion about how to resolve that problem. This works wonders when you have a rash and go to the doctor, or if you have a wicked toothache and go see a dentist. These consultations typically result in near instantaneous relief of a problem, but for business owners that are suffering from inefficiencies, cost overruns, and other major operational problems, there is a good chance that there is a way to leverage technology and automation to eliminate any problems your organization could have.
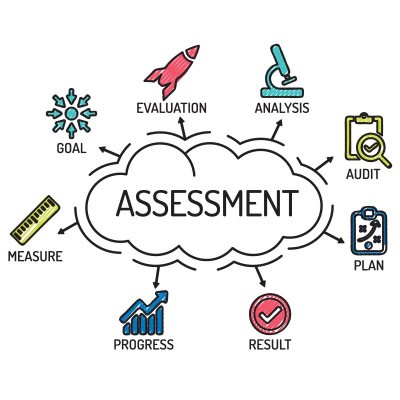
At Telesys Voice and Data, our consultants have a strong grasp on the technology the modern business uses to mitigate their inefficiencies. To that end, our consultants will perform a full network and infrastructure assessment that will give us a better idea of what kind of changes need to be made to your process, to your technology, or to your workflow.
Since you want your business to grow, we don’t just look at how you can fix the problems you have, we make a comprehensive plan on how you can leverage technology to sustain the growth you want to see and eliminate downtime and other profit-sapping inefficiencies over time. This IT roadmap can include hardware refreshes, software deployment, additions to network and physical security, and much, much more.
Our technicians understand how today’s most dynamic IT systems can work to build efficiency. We also understand that there are plenty of products on the market to help you. That’s why we put you beside some of the industry’s best vendors to get you using reliable and powerful technology to benefit your business. Best yet, the problems you have day-in and day-out with your aimless approach to technology will quickly be replaced with a strategic technology plan that works for your business. Aside from our value-based consultation service, some of the technology solutions we can provide your organization include:
- Full network and server management
- Network security monitoring
- Help Desk
- Hardware repair
- Hosted utility computing (cloud computing, hosted communications, etc.)
- Line-of-Business software (consumer relationship management, enterprise resource planning, etc.)
- Physical security solutions (access control, security cameras, etc.)
If you think you can get more out of your business, you are probably right! Call Telesys Voice and Data at (800) 588-4430 today to make an appointment to meet with one of our knowledgeable representatives and get consulted on how to best move your business forward.
There are some tasks that are essential to the health of your business’ network. For example, you need to make sure that you are engaging in regular network management activities. Do you know what this task entails?
It doesn’t matter if you’re a small business, a large enterprise, or if you're in a rural town, or a larger city. You still have to worry about the security of your data and the integrity of your infrastructure. Thankfully, there are services out there that allow even small businesses to leverage powerful, enterprise-level tools for maximum network security. The most valuable of all is perhaps the Unified Threat Management (UTM) tool.
Every business is searching for ways to improve productivity. There are now quite a few methods being used to boost the amount that each employee can accomplish, many of which revolve around technology. Admittedly, some of these methods may not be attainable for the average SMB… yet. However, as technology advances you may find yourself able to leverage some of these productivity-enhancing tools to improve the look of your bottom line.
Someday, You Could Have Smart Desks
For instance, smart desks. By connecting to the company’s local-area network, these Internet-of-Things workstations can track the behaviors of your employees to help improve their health. We’ve all heard that it is better for the human body to stand up than sit at their desks, but how many people actually do? A smart desk helps to solve this problem by alerting its occupant when to stand. Furthermore, smart desks can serve as a health monitor for an employee, allowing health issues to be caught preventatively, potentially reducing time out of the office and the amount of missed productivity.
On the topic of furniture, offering employees adjustable office furniture to use will reduce the amount of discomfort employees will experience as they attend to their responsibilities.
Yes, Television Can Be More Than a Distraction
If handled correctly, keeping a few televisions in the office can be a benefit to your employee’s productivity. After all, they don't necessarily have to be playing an afternoon soap opera or reality show. Use a television to display important company matters, like upcoming meetings, deadlines, KPIs, sales wins, and other business subjects to keep goals and deadline top-of-mind for employees. In fact, these displays can even help to inspire a little friendly competition in the office, as different departments see each other being more productive and feel the need to measure up.
There’s also a lot to be said about the value of video conferencing. If an employee needs to be two places at once--like in a critical meeting while also across the country attending an important conference--a video conferencing program can allow them to do both.
Work Smarter to Work Harder
Of course, there are plenty of other tools available to make being productive a simpler prospect for your employees. Automation can eliminate manual tasks to free up resources. After all, the more time an employee has to spend initiating a data backup or some other day-to-day. critical, but time-consuming task, the less time they can spend producing some benefit for the company.
It is also crucial that your employees are working with the solutions that will benefit their productivity the most. This means that they aren’t dealing with outdated hardware and software that experiences issues and hang-ups, and are equipped with the means to achieve optimal output. Ensuring that your technology is up-to-date and well-maintained can have a big impact to how well they work, and as a result, how well your workforce can do their jobs.
For help with creating a plan that ensures maximum productivity for your entire office, reach out to Telesys Voice and Data. We can help you implement the necessary components to ensure your office remains productive. Give us a call today at (800) 588-4430.
If there’s any experience that’s universally shared by the modern worker, it’s the sensation that there aren’t enough hours in the day. Fortunately, there are some habits that can be developed that can help to mitigate these feelings by enhancing productivity. For this week’s tip, we’ll discuss some of these practices to help boost your office’s time management capabilities.
Some organizations want to better understand the process that they use to take backups of their data and restore them in the event of an emergency. This is great, because the value of being able to do so cannot (and should not) be understated. A proper data backup and disaster recovery system could be all that stands between prosperity and failure.
Putting together your workforce is something that requires painstaking attention to detail. You found workers who are willing to work as hard as possible to further your organization’s goals. Yet, you have to remember that even the most perfect employees are still human, and that they can make mistakes and can put the organization’s data at risk. User error is a common problem, and it is one of the most important things to keep in mind while you set up your information systems.
The Internet of Things has been growing rapidly, and with this growth it has become a major part of daily life. There are connected devices you couldn’t even fathom being needed, but some have turned out to be exceeding useful. In 1977, the release of Star Wars saw people’s imaginations expand. The science end of the sci-fi went into overdrive, and soon communications and computing would change forever. Despite being a long time ago in a galaxy far, far away, the Star Wars universe introduced several concepts of the Internet of Things, decades before the IoT was even conceptualized. This week, we will take a look at the modern day Internet of Things, and how Star Wars primed us for our own future.
If you use Google Drive as your preferred cloud provider, you know that it’s a dynamic service that offers everything from word processing to spreadsheets to file storage. However, there are many other ways to use Google Drive that you may not even be aware of. Here are three secret tips that can help you get a little more value out of Google Drive.
It’s time to face the fact that those times when your technology acts up, you don’t have the time to spare waiting around for the issue to just go away...you need to react. Many small businesses just don’t have the means to maintain an in-house IT resource to solve their problems. What if we can offer you a different solution.
In order to function properly, any business will need to procure certain pieces of equipment. Some of this equipment will be specialized to the business’ purpose, while some will be the sort that may be more commonly found in offices everywhere. This equipment must be procured from somewhere, and this is where vendors come in--but who in your organization is responsible for your vendor management?
Phishing attacks have been around for decades, first being recorded in 1995 where scammers would pose as AOL employees and request a user’s billing information through instant messages. Nowadays, email phishing attempts have tricked users into handing over personal information of all kinds. There are many methods of identifying a phishing attempt, but today we’ll focus on one.
The Internet is always changing, and anyone who has been using it for a while has experienced this change for themselves. While it might be strange to think about, the latest statistics have proven that the current changes to the Internet are some of the most significant--especially for businesses. “Online business as usual” will be significantly different moving forward.
With technology being deployed to help businesses solve all manners of operational inefficiency, it’s often difficult to pinpoint what IT will work best for your business. Organizations of all types look to technology; and, at some point you need to ask yourself if your technology is set up to help reach your business’ potential.
Smartphones, laptops, and Chromebooks empower today’s workforce to be more mobile, and employees are often the driving force behind this. Chances are, if your business hasn’t even begun to think about your mobile IT strategy, a percentage of your staff already has.
Computers are great tools to get work done in the office, but only if they are used effectively. Employees looking to get more out of their Windows workstations can utilize the taskbar to get around faster. We’ll discuss some of the ways your business can take better advantage of the taskbar, as well as what it’s capable of.
With the smartphone market losing ground for the first time in its short history, many of the manufacturers you’ve come to know are either non-factors in the current market, or don’t even produce smartphones anymore. With new demand growing every year, new manufacturers such as OnePlus and Xiaomi are primed to fall in line behind Samsung and Apple.
Consider for a moment how many documents are floating around your business at any given point. Memos, notes, invoices, receipts, and whatever else you happen to accumulate in the course of business, all floating around the office. This isn’t a great approach, and unfortunately, the classic solution for this, the filing cabinet, isn’t the most effective solution anymore.
How does your organization manage its mission-critical technology solutions? We know that most small businesses have some sort of trouble with this topic, either due to budget constraints or a lack of personnel. Either way, we know that there is a better way to manage your business’ technology, and it’s all thanks to an approach called managed IT services.
Mobile? Grab this Article!
Tag Cloud